- Dogs of Fire
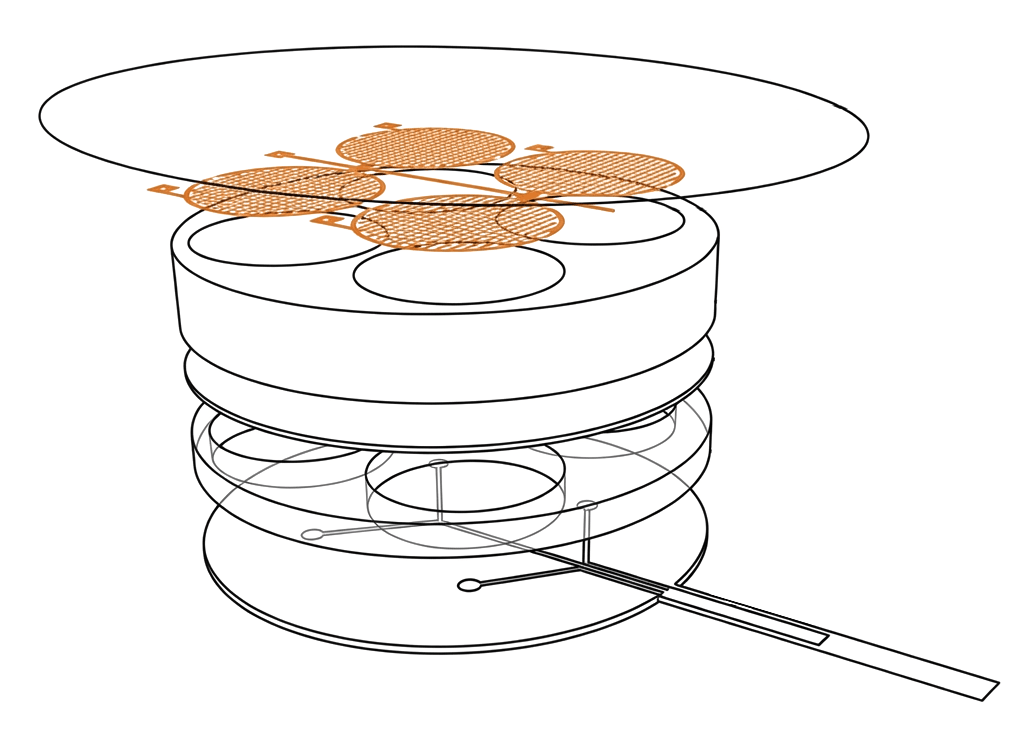
Voice to Skull Technology
EVERYTHING THEY USE AGAINST YOU — NOW IN YOUR HANDS
100%
Documented — every technique, every tactic, every psychological pattern. No speculation.
90%
Of targeted individuals never understand what’s happening to them. This book changes that.
mind control technology
Whether you’re a targeted individual trying to make sense of what’s happening, a researcher investigating covert harassment programs, or simply a curious mind who senses something is deeply wrong with the world — Dogs of Fire was written for you. This is not a conspiracy theory book. This is a field manual.
Dogs of Fire
The beginning of the organization and its current nature
Express quotes – often on the same day Two-stage technical feasibility check Flexible offer optimization regarding price or delivery time
Target's life
Targeted individuals are people who report being the subjects of organized, covert harassment campaigns. They experience coordinated surveillance, psychological operations, electronic harassment, social isolation, and reputation attacks. This book provides the tools to document, understand, and respond to these experiences.
Manipulation and exploitation of trauma
“The Psychological Architecture of Gang Stalking: How It’s Built and How It Breaks You”
Psychological methods and techniques
Dogs of Fire doesn’t just expose the machinery of organized targeting — it hands you the keys to understand it, survive it, and dismantle it. Chapter by chapter. Tool by tool. this book breaks down every method used against you in language anyone can understand.
Devices and Mind Mapping
Modern gang stalking increasingly leverages algorithmic tools: data aggregation, behavioral profiling, location tracking, and coordinated digital campaigns. This chapter is the first comprehensive treatment of how digital infrastructure is weaponized against targeted individuals.
Electronic Harassment & Surveillance
Electronic harassment includes unauthorized surveillance, device tampering, social media manipulation, algorithmic shadow-banning, and more advanced forms of digital intrusion. This chapter explains the technical methods in accessible language for all readers.
Behavioral suggestion and justification of the source of symptoms
Receive real-time production status updates for your orders at your convenience—access exclusive part photos and comprehensive inspection data even before your items are delivered.
Correcting misconceptions
Gang stalking is surrounded by misinformation — ranging from systematic disinformation and distortion of the truth to accounts of experiences driven by fear and pain. This book debunks many common myths with fact-based and evidence-based responses.
The right ways to confront
Millions of people around the world report the same experience: surveillance, harassment, psychological pressure, and social sabotage. Dogs of Fire names it, maps it, and arms you with the tools to reclaim your life. “From Victim to Victor: The Mental Recovery Roadmap for Targeted Individuals”
- Dogs of Fire
No jargon. No agenda. Just answers.
Those most affected by secret targeting programs have long been ignored, misdiagnosed, and isolated. This book changes that, by placing documented knowledge directly into the hands of those who need it most and empowering them to make their experience a source of meaningful information rather than a source of ridicule and alienation.
The book faced many obstacles and difficulties until God enabled us to publish it for the general public.
Whether you’re a victim trying to understand what’s happening, a researcher investigating covert harassment programs, or simply a curious individual who feels something is seriously wrong, Dogs of Fire is for you. This isn’t about conspiracy theories; it’s a practical guide. Every piece of information is based on documented research, declassified government programs, and verifiable case studies. We cite our sources and provide evidence.
- Dogs of Fire
We see what you see, hear what you hear, and all your movements are what we want.
“Understand exactly what is being done, how it works, and why you were never supposed to figure it out.”
Turn Your Knowledge Into a Force Against Misinformation
- Send us a summary of what you learned from each section or the misconceptions that were corrected, because the book faced a number of restrictions, and we are keen to know whether you obtained the original copy or not.
- You can support the project by providing your feedback to help establish a force that fights against misinformation.
